Access control is one of the most essential cybersecurity practices. Meticulous management of user access rights helps to secure sensitive data and reduces the chance of a successful attack.
However, choosing an access control model relevant to your organization can be tricky. This article discusses use cases for mandatory access control (MAC) and discretionary access control (DAC) models. We also show the difference between DAC and MAC to help you choose one over the other. Finally, we provide tips on implementation.
Access control models: why are they important?
Access control regulates which users, applications, and devices can view, edit, add, and delete resources in an organization’s environment. Controlling access is one of the key practices for protecting sensitive data from theft, misuse, abuse, and other threats. There are two levels of access control: physical and logical.
Access control helps mitigate both internal and external threats. That’s why IT regulations, laws, and standards — NIST, HIPAA, PCI DSS, and others — enforce strict physical and logical access control measures. In this article, we discuss models of logical access control.
You can choose from several logical access control models, including mandatory, discretionary, role-based, and attribute-based. Each model has its pros and cons. Later in this article, we’ll review the pros and cons of MAC and DAC. For more on this topic, read our article about the pros and cons of role-based access control and attribute-based access control models.
The process of selecting one of these models differs from organization to organization. The choice of model depends on:
- The nature of the protected data
- IT requirements and industry standards
- The number of employees
- The cybersecurity budget
Let’s learn the specifics of each model to find out when using MAC is better than using DAC and vice versa.
Insider Threat Management with Syteca
What is mandatory access control?
Mandatory access control (MAC) is a model of access control where the operating system provides users with access based on data confidentiality and user clearance levels. In this model, access is granted on a need-to-know basis: users must prove their need for information before gaining access.
MAC is also called a non-discretionary access control model, which means that control isn’t granted at the discretion of the user or file owner. The control mechanisms of the MAC model enable organizations to implement zero-trust principles.
MAC is considered one of the most secure access control models. Access rules in this model are manually defined by system administrators and strictly enforced by the operating system or security kernel. Regular users can’t alter security attributes even for data they’ve created.
What are the basic principles of MAC?
- The utmost privacy and confidentiality of the organization’s resources are paramount. No one has default privileges to access or edit someone’s data.
- Access provisioning is centrally administered.
- Each individual and resource in the system has security labels with their classification and category.
With MAC, the process of gaining access looks like this:
- The administrator configures access policies and defines security attributes: confidentiality levels and clearances for accessing different projects and types of resources.
- The administrator assigns a set of attributes to each subject (user or resource that accesses data) and object (file, database, port, etc.).
- When a subject attempts to access an object, the operating system examines the subject’s security attributes and decides whether access can be granted.
- To obtain access to the object, the user provides their credentials.
In addition to checking confidentiality and clearance levels (classification matches between subject and object), operating systems pay attention to category matches between subject and object. A “top secret” classification doesn’t automatically provide a user full access to a file if they aren’t a member of the required category for the object.
Let’s take a look at an example of mandatory access control implementation. Assume that an organization possesses data with a “top secret” confidentiality level and an “engineering project” security label. This data is available only to a set of users with both a “top secret” security clearance (classification) and authorization to access engineering documents (category). Such users can also access information that requires a lower level of clearance. At the same time, employees with lower clearance levels or no rights to access engineering documents can’t access such information.
MAC brings many benefits to a cybersecurity system, but it also has several disadvantages. Let’s look at the advantages and disadvantages of mandatory access control.
Pros and cons of MAC
Pros
- High level of data protection — An administrator defines access to objects, and users can’t alter that access.
- Granularity — An administrator sets user access rights and object access parameters manually.
- Immunity to Trojan Horse attacks — Users can’t declassify data or share access to classified data.
- Fewer errors — Strict and constantly controlled policies help reduce system errors that lead to over-privileged users.
- Strict division — Admins divide users into subsets and limit resource exposure for these subsets using security attributes.
Cons
- Complex maintenance — Manual configuration of security levels and clearances requires constant attention from administrators.
- Manual scalability — MAC doesn’t scale automatically. New users and pieces of data demand constant updates on objects and account configurations.
- Interference with workflow — Users have to request access to each new piece of data; they can’t configure access parameters for their own data.
When to use MAC
This access control model is mostly used by government organizations, militaries, and law enforcement institutions. The US government uses MAC to secure classified information and to support multilevel security policies and applications. For better data protection and compliance in the insurance industry and the banking sphere, organizations use MAC to control access to customer account data. This type of non-discretionary access control model can also protect access to databases, where procedures, tables, views, and other elements are the objects.
It’s reasonable to use MAC in organizations that value data security more than operational flexibility and costs. Implementing MAC in a private organization is rare because of its complexity and inflexibility.
A purely MAC model provides a high and granular level of security. On the other hand, it’s difficult to set up and maintain. That’s why it’s common to combine MAC with other access control models.
For example, combining it with a role-based model speeds up the configuration of user profiles. Instead of defining access rights for each user, an administrator can create user roles. Each organization has users with similar roles and access rights: employees with the same job position, third-party vendors, etc. An administrator can configure roles for these groups instead of configuring individual user profiles from scratch.
Another popular combination is MAC and the discretionary access control model, or DAC. MAC can secure sensitive data, while DAC allows coworkers to share information within a corporate file system.
Request access to the online demo of Syteca!
See how Syteca can help you manage user access to your organization’s systems and data.
What is discretionary access control?
Discretionary access control is an identity-based access control model that gives users some control over their data. Data owners (document creators or any users authorized to control data) can define access permissions for specific users or groups of users. In other words, whom to give access to and what privileges to grant are decided at the resource owner’s discretion.
Access permissions for each piece of data are stored in an access-control list (ACL). An administrator creates this list when a user grants access to somebody. The list can be generated automatically. An ACL includes users and groups that may access data and their access levels. A system administrator can also enforce an ACL. In this case, the ACL acts as a security policy, and regular users can’t edit or overrule it.
What are the basic principles of DAC?
- Object characteristics (size, name, directory path) are invisible to users that aren’t authorized.
- Several failed access attempts trigger additional authentication (MFA) requirements or deny access.
- Users can transfer object ownership to other users. The owner also determines the access type of other users. Based on these access privileges, the operating system decides whether to grant access to a file.
Gaining access to a file with DAC works like this:
- User 1 creates a file and becomes its owner, or obtains access rights to an existing file.
- User 2 requests access to this file. They provide their credentials: username, password, or something else.
- User 1 grants access at their discretion. However, user 1 can’t grant access rights that exceed their own. For example, if user 1 can only read a document, they can’t allow user 2 to edit it.
- If there’s no contradiction between the administrator-created ACL and the decision made by user 1, access is granted.
Discretionary access control is quite a popular model because it allows a lot of freedom for users and doesn’t increase administrative overhead. However, it has several considerable limitations.
Pros and cons of DAC
Pros
- User-friendly — Users can manage their data and quickly access the data of other users.
- Flexible — Users can configure data access parameters without administrators.
- Easy to maintain — Adding new objects and users doesn’t take much time for the administrator.
- Granular — Users can configure access parameters for each piece of data.
Cons
- Low level of data protection — DAC can’t ensure reliable security because users can share their data however they like.
- Obscure access management — There’s no centralized access management, so in order to find out access parameters, you have to check each ACL.
- Overlay of user privileges — A permissions conflict may occur for users of multiple nested workgroups.
When to use DAC
DAC shouldn’t be used by organizations that work with extremely sensitive data (medical, financial, military, etc.) for several reasons:
- If user 1 shares access rights with user 2, there’s no guarantee that user 2 needs this access to work, won’t steal or corrupt data, and won’t grant access to a malicious user.
- It’s impossible to control information flows inside the network.
- It’s impossible to enforce the principles of least privilege, need to know, and separation of duties.
At the same time, DAC is a good choice for small businesses with limited IT staff and cybersecurity budgets. It allows for the sharing of information and ensures the smooth operation of the business. When applied in an organization with 10 to 20 employees, DAC presents less complexity and oversight challenges compared to using it in organizations with hundreds or thousands of employees.
Explore the power of Syteca now!
Test how Syteca can help you secure access to critical systems and data.
MAC vs. DAC: Comparison table
Below, we review the key characteristics of both models to help you easily grasp the differences between DAC and MAC.
DAC and MAC differences
Characteristic
MAC
DAC
Access control enforced by
MAC
Administrators and operating system
DAC
Administrators and users
Form of access control policy
MAC
Confidentiality levels and clearances
DAC
Access-control lists with user identities
Maintenance
MAC
Hard
DAC
Easy
Implementation cost
MAC
High
DAC
Low
Granularity
MAC
High (admins adjust clearances for each user and object manually)
DAC
High (users can assign access rights to any other user or group)
Security level
MAC
High
DAC
Low
Useful for
MAC
Government, military, law enforcement
DAC
Small and medium-sized companies
Trusted users
MAC
Only administrators
DAC
All users
Baseline for gaining access decisions
MAC
Tasks and objects that have their own IDs
DAC
Ownership and user IDs
DAC and MAC differences
Comparing DAC vs. MAC access control models in this way demonstrates that they’re different in almost every aspect and suitable for different kinds of organizations. DAC works well for organizations that require flexibility and user-friendly workflows. On the other hand, MAC is more suitable for organizations that work with highly sensitive data.
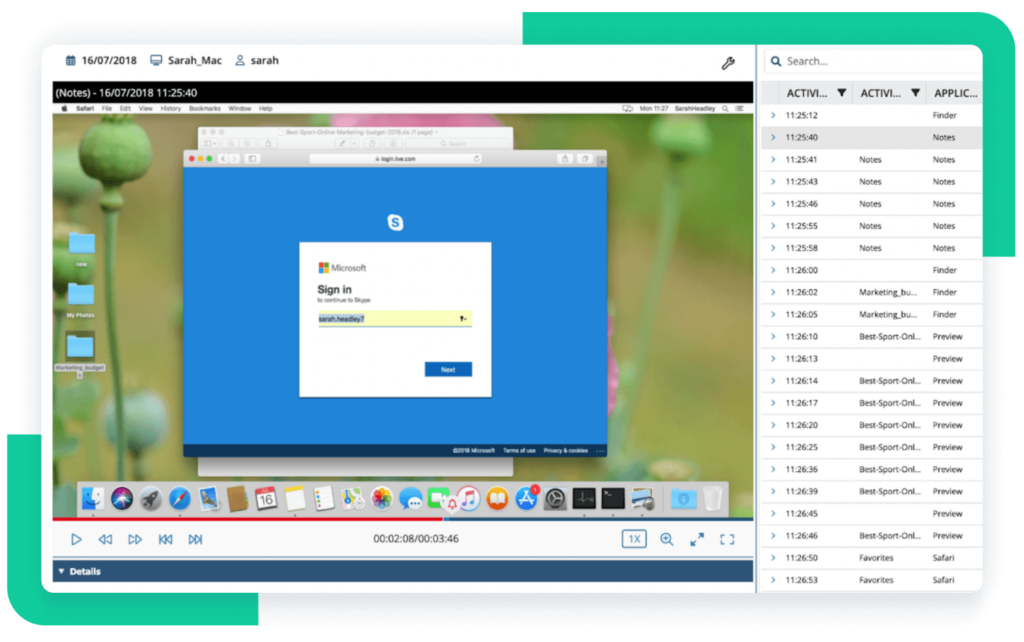
Privileged Access Management with Syteca
Implement robust and flexible access management with Syteca
Many organizations require elements of both discretionary access control and mandatory access control models. The flexibility, scalability, and simplicity of DAC are important for creating a simple and uninterrupted workflow. At the same time, organizations might need the high level of security and granularity offered by the MAC model.
Are these characteristics crucial for your organization? Syteca’s access management functionality can help you get the best of MAC and DAC with an all-in-one platform. We offer a wide range of access control possibilities:
- Identity management — Automate and secure user authentication to reduce the risks of unauthorized or malicious access.
- Two-factor authentication — Confirm user identities by prompting users to enter additional one-time passcodes sent to their mobile devices.
- Secondary authentication — Request users to enter additional credentials after logging in to distinguish their activity in critical administrative and other shared accounts.
- Password management — Advance your secrets management strategy by automating password provisioning and rotation, and enabling employees to create and share their own passwords.
- Privileged access management — Сontrol user privileges and monitor privileged user sessions to ensure users handle your organization’s most sensitive data securely.
- Access request and approval workflows — Enable your admins to approve user requests for access to protect your most critical resources properly.
Conclusion
After comparing DAC and MAC, we can clearly see that they fall on opposite ends of the access control spectrum. MAC is controlled by administrators and requires lots of time and effort to maintain, but it provides a high level of security. DAC is much easier to implement and maintain, as users can manage access to the data they own. However, DAC doesn’t measure up when it comes to protecting sensitive records.
Syteca allows you to combine the benefits of both of these access control models. The platform’s password management, one-time passwords, time-based user access restrictions, and manual access approval functionalities can help you enforce a flexible yet secure access management process.